Kerberos
Just another introduction to Kerberos
Kerberos
Just another introduction to Kerberos
Introduction to Kerberos
Kerberos is a network authentication protocol that provides secure, single sign-on (SSO) access to services within an Active Directory (AD) environment. It enables users to authenticate once and then access multiple services without re-entering credentials. Kerberos is widely used in enterprise settings due to its strong encryption and mutual authentication mechanisms, preventing password transmission over the network in plaintext.
At its core, Kerberos federates authentication and authorization to services within an Active Directory (AD) domain. This means that instead of each service handling authentication separately, a centralized Key Distribution Center (KDC) within the domain authenticates users and issues tickets, which services trust for user access.
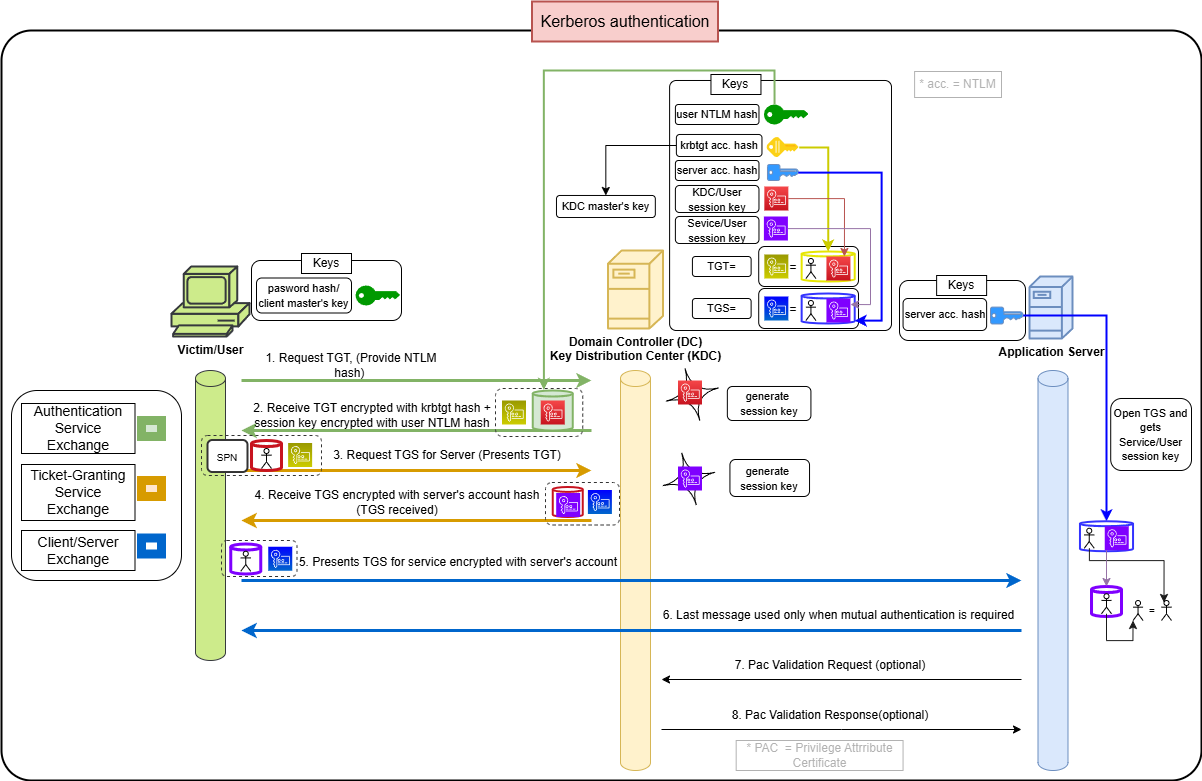
This article provides a detailed explanation of the Kerberos authentication process using the diagram below.
Kerberos Authentication flowchart with descriptions of messages and keys
Understanding the Kerberos Authentication Flow
The diagram illustrates the step-by-step process of how a user authenticates to a Kerberos-enabled service. Let’s break it down step by step.
1. Authentication Service Exchange
- User Requests a Ticket Granting Ticket (TGT)
- The user submits an authentication request to the KDC .
- This request includes the username and an encrypted timestamp using the user’s password hash (NTLM hash) .
- KDC Issues a TGT (Ticket Granting Ticket)
- The KDC verifies the user’s identity and generates a TGT , encrypted using the krbtgt account’s hash.
- The TGT also contains a session key , encrypted using the user’s NTLM hash .
- The user stores the TGT in memory for future authentication requests.
2. Ticket Granting Service (TGS) Exchange
- User Requests a Service Ticket (TGS)
- When accessing a service (e.g., a file share or SQL database), the user presents the TGT to the KDC and requests a TGS for the specific service.
- The request includes the Service Principal Name (SPN) of the target service.
- KDC Issues the Service Ticket (TGS)
- The KDC generates a new session key (Kc,s) for the client-service interaction.
- It then creates a TGS , which is encrypted with the target service’s NTLM hash .
- The client receives both the TGS and the session key (Kc,s) , which it will use to communicate securely with the service.
3. Client/Server Exchange
- User Presents the Service Ticket (TGS) to the Target Service
- The user sends the TGS to the application server.
- The service decrypts the TGS using its own NTLM hash .
- The service extracts the session key (Kc,s) and uses it to establish a secure session with the user.
- Mutual Authentication (Optional)
- If mutual authentication is required, the service sends back a response to prove its identity to the user.
4. PAC Validation (Optional Security Step)
- Service Requests PAC Validation from KDC
- Some services (e.g., SMB, MSSQL) require Privilege Attribute Certificate (PAC) validation .
- The service sends the PAC extracted from the TGS to the KDC for validation .
- KDC Responds with PAC Validation Status
- If the PAC is valid , the service grants access.
- If validation fails, access is denied.
Key Components in the Diagram
- Victim/User: The client machine requesting authentication.
- Key Distribution Center (KDC): The centralized authentication server in AD.
- Application Server: The target service the user is trying to access.
- NTLM hash (aka acc. in the image): the credential identifying the user
- TGT (Ticket Granting Ticket): A temporary authentication token issued by the KDC.
- TGS (Service Ticket): A ticket used to access a specific service.
- Session Key (Kc,s): A key used to secure communication between the client and the service.
Why is Kerberos Secure?
Kerberos improves security in Active Directory by:
- Preventing password transmission over the network (authentication is done using encrypted tickets instead) .
- Ensuring mutual authentication (both users and services verify each other’s identity) .
- Using session keys to encrypt data and prevent replay attacks.
- Enforcing PAC validation to prevent privilege escalation attacks.
Final Thoughts
Kerberos remains a foundational authentication protocol in enterprise environments, especially in Active Directory. Understanding its flow and security mechanisms is critical for both red teamers (attackers) and blue teamers (defenders) looking to protect an organization’s authentication infrastructure.
Would you like to dive deeper into Kerberos attack techniques like Kerberoasting or Pass-the-Ticket attacks? Let us know in the comments! 🚀
Post converted from Medium by ZMediumToMarkdown.