Diffie-Hellman Key Exchange
in color
Diffie-Hellman Key Exchange in Color
Key Exchange algorithms help in establishing a private channel over a public channel.
In this post we are going to see a simple yet effective explaination of the Diffie-Hellman Key Exchange (DHKE) protocol using colors.
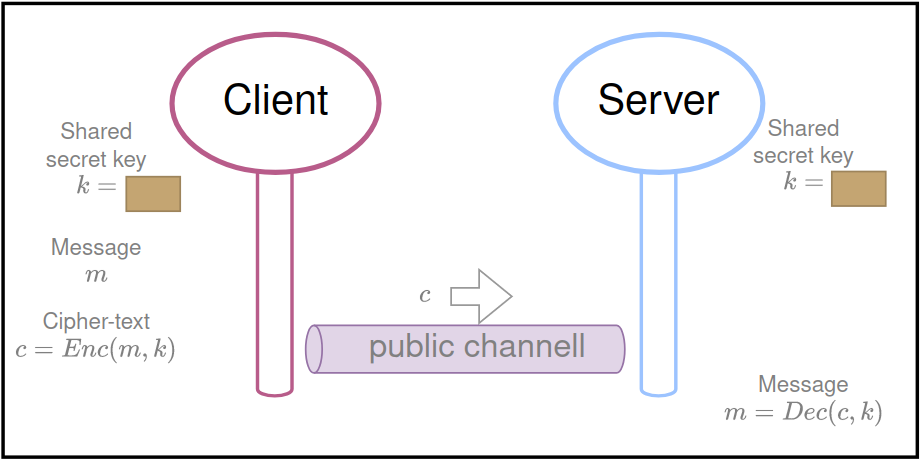
Symmetric Key encryption
Two parties (e.g., a Client and a Server) that know a shared secret can build a private communication channel thanks to symmetric cryptography.
sharing a secret is sufficient for exchanging messages as in a private channel
In 1976, Whitfield Diffie and Martin Hellman devised a great trick to exchange secrets over a public channel, this method is also known as a Key Exchange algorithm
To sketch the idea, we are going to use a famous analogy with colors.
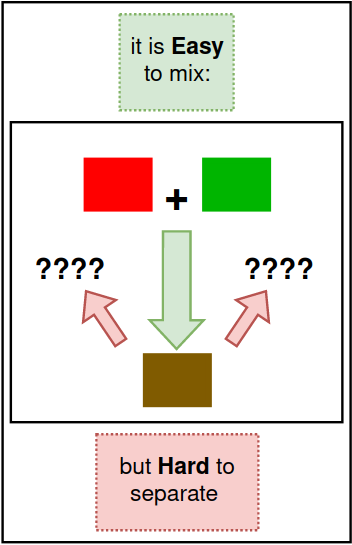
Preliminary concept
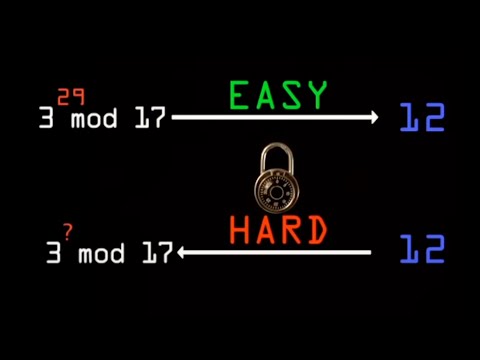
Think of mixing colors as a “ one-way ” process:
- it is easy to mix them
- but hard to separate in the exact original colors
(the symbol “+” is a placeholder for the mixing operator)
The one-wayness of mixing colors
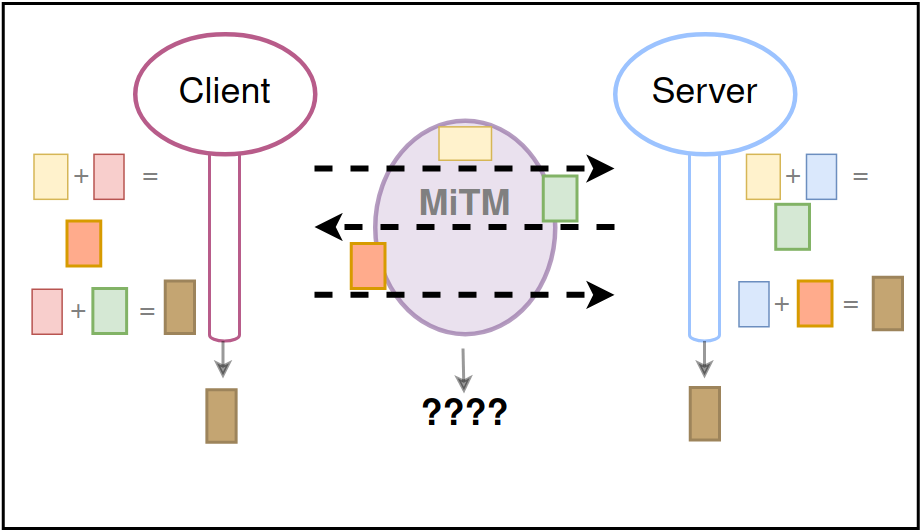
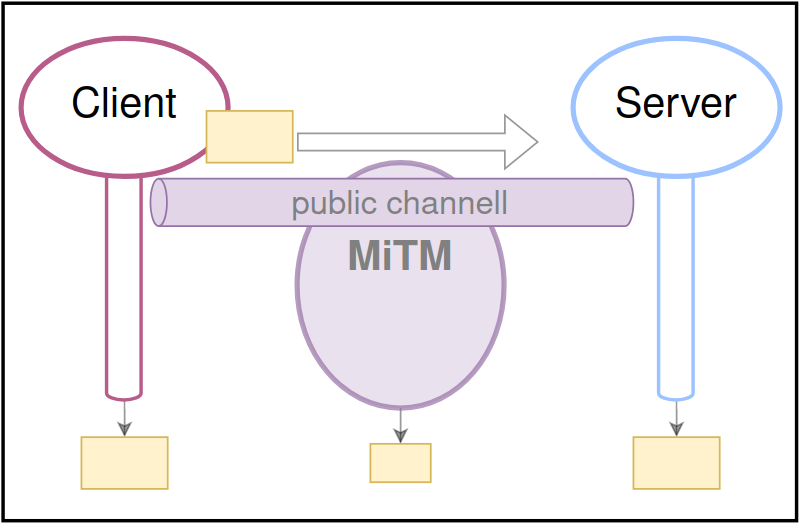
How could Client and Server exploit this to agree on a secret color hiding from a Man in The Middle (MiTM) that is eavesdropping on the public channel?
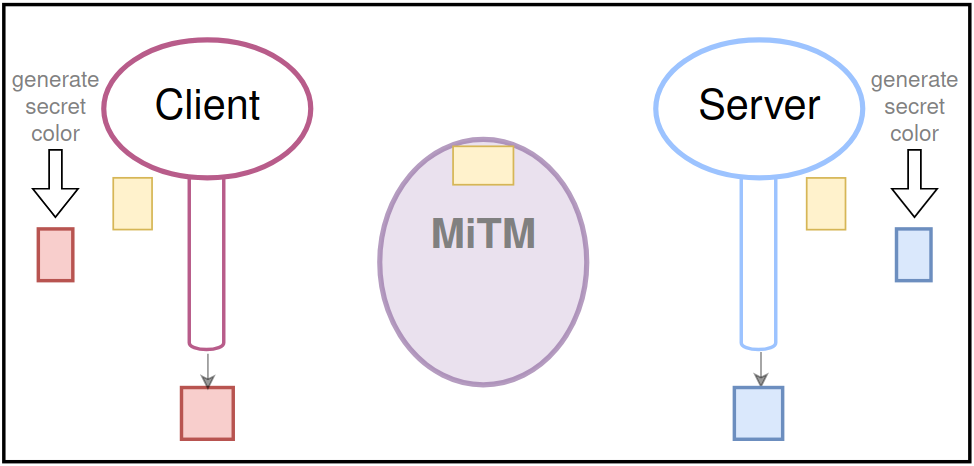
- First Client and Server agree on a public color, let’s say YELLOW. (to agree to yellow, it’s sufficient that one sends the other, as in the symmetric key example also the MiTM obtains it)
In the next rounds, Client and Server generate their secret colors, say RED for the Client and BLUE for the Server,
then the parties mix their private color with the public color YELLOW respectively, and send the resulting color to the other:
The parties mix their private color with the public one and exchange the result
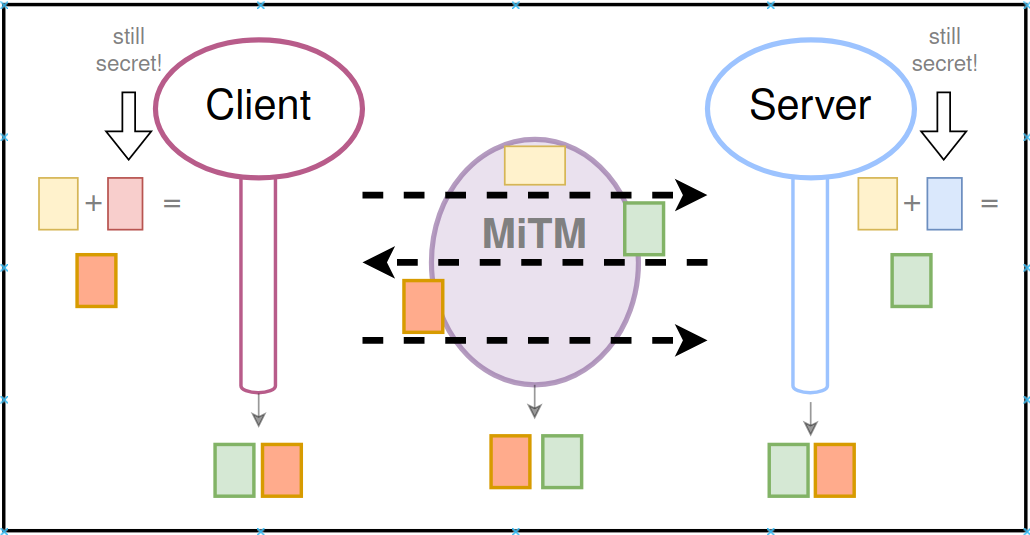
- The Client sends ORANGE
- The Server sends GREEN
- Both these colors are now known also to the MiTM, which should not be able to obtain the respective secret colors (thanks to the one-wayness of mixing)
Now Client and Server mix the color they received from the other party to their secret one , obtaining the same shared color (BROWN), unknown by the MiTM.
So they can use it as a symmetric session-key for exchanging messages thanks to symmetric cryptography.
In a following post we will look at the math behind it.
Conclusions
DHKE is a usefull tool for generating secrets between authenticated entities, but it is susceptible to impersonation attacks in case the communication link is unauthenticated.
References
Post converted from Medium by ZMediumToMarkdown.